As the digital frontier continues its rapid expansion, our underlying network protocols must adapt to stay at pace. A crucial development related to this is the shift from IPv4 to IPv6, an essential move to accommodate the explosive growth in internet-enabled devices. Yet, alongside its enhanced capabilities, IPv6 introduces ...
Ethical hacking is a structured, multi-stage process designed to assess and improve an organisation’s cybersecurity posture. At its core, it mirrors the tactics of malicious hackers, but applies them within a legal and authorised framework. Among the earliest and most crucial stages of this process are reconnaissance and its ...
Identity and Access Management (IAM) is a foundational pillar of modern cybersecurity. As organisations expand their digital footprints, ranging from adopting cloud services to mobile workforces and machine identities, IAM is the mechanism that enforces who can access what, when and how.
IAM is also one of the core domains ...
Cryptography stands as one of the most critical pillars in modern cybersecurity. It serves as the foundation for securing digital communication, transforming readable data (plaintext) into unreadable formats (ciphertext) to shield it from unauthorised access. Just as importantly, it facilitates the reverse process called decryption to ensure that the ...
Remote work has become the primary workplace environment for many organisations today, offering flexibility, broader talent pools, and increased autonomy. However, with these benefits come unique challenges, particularly in project management. For leaders managing dispersed teams, navigating remote workflows often requires a fresh perspective and new strategies.
This article explores ...
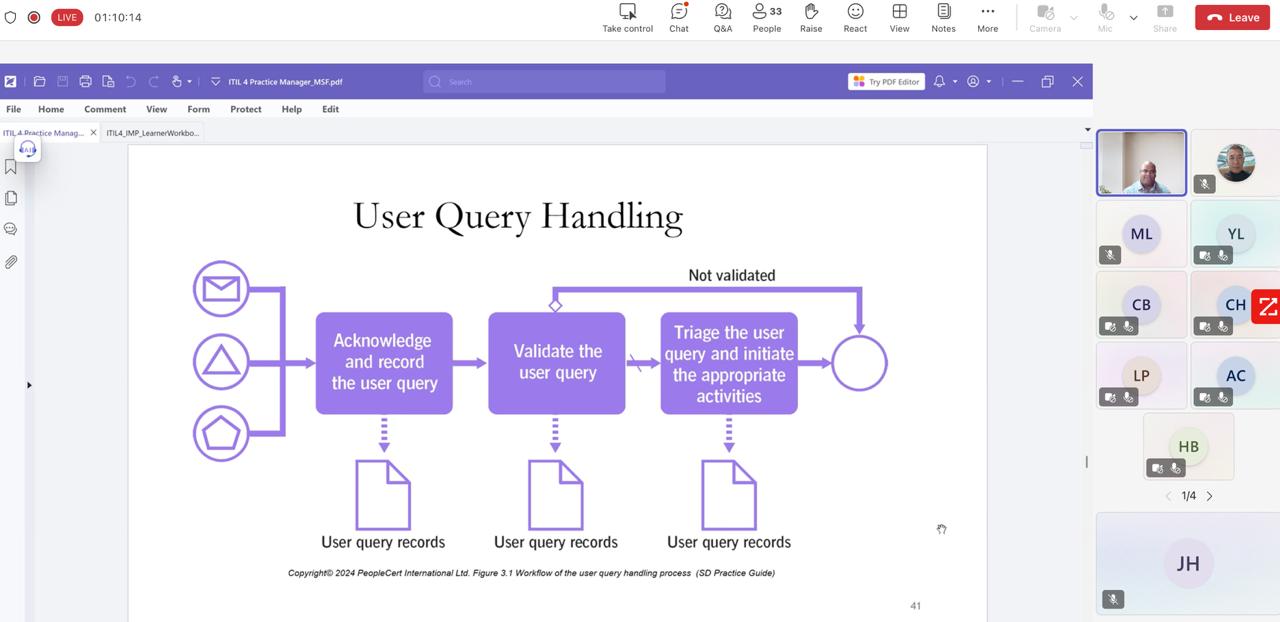
Recap of ITIL® 4 Monitor, Support & Fulfil Webinar: practical ITSM insights, certification pathways, and an interactive quiz with prizes
Today, everyone knows what AI is and how its current state has become advanced enough to the point that it’s disrupted almost every industry out there, including project management. Indeed, as AI continues to become better and more powerful, the name of the game moving forward will be finding ...
Every time you access your digital bank, stream content, or make a secure payment, there's a system working behind the scenes to keep your online activities safe: Public Key Infrastructure (PKI). This complex framework underpins the trust and security that make today’s digital communications possible. From encrypting sensitive data ...
In project management, technical know-how and organisational skills are essential, but so is the human element. Managing stakeholders effectively is often the difference between a successful project and one that falls apart under competing demands. A frequently underestimated yet critical component of stakeholder management is learning how—and when—to say ...
Mastering scripting languages is essential for anyone serious about web hacking and penetration testing. Unlike compiled languages, scripting languages interpret code line-by-line at runtime with no compiler required. This makes them agile, portable, and perfect for hands-on security work.
Compiled languages, like C or Java, need a compiler to translate ...